Anonymous unmasked: hacker ringleader turned FBI informant
Loading...
"Anonymous," the hacker group, is no longer anonymous.
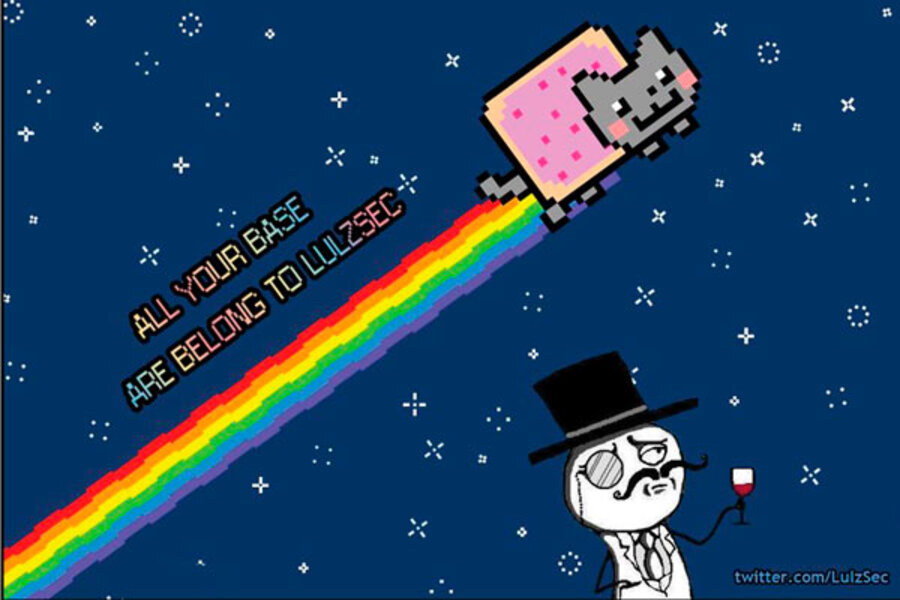
Six people alleged to be operating under the moniker of Anonymous, as well as "LulzSec" and "Internet Feds" – who had used their cyberskills to invade with seeming impunity computers belonging to law enforcement, government, and business – were arrested Tuesday.
Hector Xavier Monsegur, an unemployed computer programmer reportedly living on welfare in New York, was the ringleader operating under the name "Sabu," federal authorities say. He pleaded guilty to a dozen computer crimes including conspiracy. But the indictment handed down by the US Attorney of New York's southern district also said he cooperated with authorities to help round up other high-level hackers during a months-long investigation.
Monsegur's journey from elite hacker to FBI informant began in 2008, when a loose confederation of computer hackers known as Anonymous were hacking into the websites and computer databases of companies and organizations they disliked, according to a statement by the Federal Bureau of Investigation's New York City office.
For example, between December 2010 and June 2011 Mr. Monsegur and other members of Anonymous were responsible for cyberattacks against the websites of Visa, MasterCard, and PayPal. The attacks were retaliation for those companies' refusal to process donations to WikiLeaks, the website that has drawn criticism for publishing secret government documents.
Sometime around the end of 2010, Monsegur was invited by another hacker – not named as a defendant – to join Internet Feds, a group of elite computer hackers affiliated with Anonymous, according to the indictment.
Monsegur was invaluable to the group as a "rooter," or someone who identifies vulnerabilities in the computer systems of potential victims in order to exploit those systems and gain access to them, the indictment said. He also provided "infrastructure support" – unauthorized access to computer servers and routers that others could use to launch cyberattacks.
After joining Internet Feds, Monsegur and his fellow elites hacked at will into computer systems belonging to Fox Broadcasting Company, PBS, and Sony, among others.
From Fox, he is alleged in early 2011 to have stolen confidential information relating to contestants on the "X-Factor" television show. From Sony Pictures, he is alleged to have stolen confidential release dates of music and details of security vulnerabilities in the company's Russia operations. At the start of the Arab Spring revolution in 2011, Monsegur is alleged to have hacked into government systems belonging to Tunisia, Algeria, Yemen, and Zimbabwe.
Building on the publicity generated by these hacks, Monsegur and other hackers formed a new hacking group called Lulz Security, the FBI said in its statement. His partners included at least four other individuals named in Tuesday's indictment: Ryan Ackroyd ("Kayla") and Jake Davis ("Topiary”) of Britain, and Darren Martyn (“pwnsauce”) and Donnacha O'Cearrbhail (“palladium”) of Ireland.
Along the way, Monsegur was paying bills. He is alleged to have stolen banking credentials, credit card numbers, and other data he used to purchase items – and shared the stolen information with others. At one point, he hacked into an auto parts supplier and had four automobile engines worth $3,450 shipped to himself in New York City.
Another person charged Tuesday, Jeremy Hammond of Chicago, was arrested Monday by the FBI. He is charged with hacking into Strategic Forecasting, Inc. (“Stratfor”), a global intelligence firm in Austin, Texas, in December. He may have stolen confidential information concerning 860,000 people.