Ahead of midterms, states scrambling to fend off cyberattacks
Loading...
| WASHINGTON
Last year, US intelligence and election-security experts issued grim warnings that alleged Russia-backed meddling during the 2016 election was merely a “wake-up call.” Now, four months from the 2018 midterm elections, it’s unclear if the United States is ready for another round of attacks. In March, Congress passed a measure providing a one-time grant of $380 million to state officials to upgrade and harden their election infrastructure. But while the money is welcome, analysts say it is only a starting point. For example, 14 states in 2016 were using voting machines incapable of producing a voter-verified paper record. Since then, only one – Virginia – has made the transition to a more secure system. Likewise, many specialists advocate statistics-based audits, using random samples of paper ballots, to verify election results and identify hacking attempts. But this year, Colorado will be the only state in the country using the technique. “This is a national security issue,” says Lawrence Norden of the Brennan Center for Justice in New York. “In that context, $380 million is almost nothing. That is what we spend on a single Air Force jet in some cases.”
Why We Wrote This
The security and reliability of voting systems are fundamental to democracy. Congress and many states are moving to address vulnerabilities – but experts say they are not doing nearly enough.
With the 2018 midterm elections fast approaching, security experts are warning that the nation’s election infrastructure will once again come under assault by hackers seeking to undermine American democracy.
But here’s an underappreciated fact: We’re already under attack.
“We average 100,000 scans on our [computer] systems a day,” Missouri’s secretary of state, Jay Ashcroft, told a recent Senate panel examining election security. He was referring to unauthorized probing of the networks.
Why We Wrote This
The security and reliability of voting systems are fundamental to democracy. Congress and many states are moving to address vulnerabilities – but experts say they are not doing nearly enough.
Mr. Ashcroft and other state election officials were asked how often they detect attempts specifically to break into voter-registration and other election-related systems.
“Every day,” responded Vermont’s secretary of state, Jim Condos. “We probably receive several thousand scans per day.”
Steve Simon, Minnesota’s secretary of state, compared the frequent attempted cyber-intrusions he sees to a car thief casing a parking lot. “[The car thief] goes there a day or two in a row, and takes out binoculars and observes traffic patterns, and he tries to figure out, is there a way in?” Mr. Simon told the senators.
“There are a lot of people casing a lot of parking lots,” he said.
Last year, US intelligence and election-security experts issued grim warnings that alleged Russia-backed meddling during the 2016 election was merely a “wake-up call.”
Now, four months from the 2018 midterm elections, it’s unclear if the US is ready for another round of election-related attacks in the cyber-shadows.
“There is a vast improvement over where we were in 2016,” says Lawrence Norden, an election expert at the Brennan Center for Justice in New York. “There has been so much more discussion and training done over the last year and a half than there ever was around cybersecurity.”
But, he adds, it is not nearly enough.
In March, Congress passed an election-security measure to provide a one-time grant of $380 million to state officials to upgrade and harden their election infrastructure.
While the money is welcome, analysts say it is only a starting point to address the full spectrum of vulnerabilities exposed during the 2016 election season.
“This is a national security issue,” Norden says. “In that context, $380 million is almost nothing. That is what we spend on a single Air Force jet in some cases.”
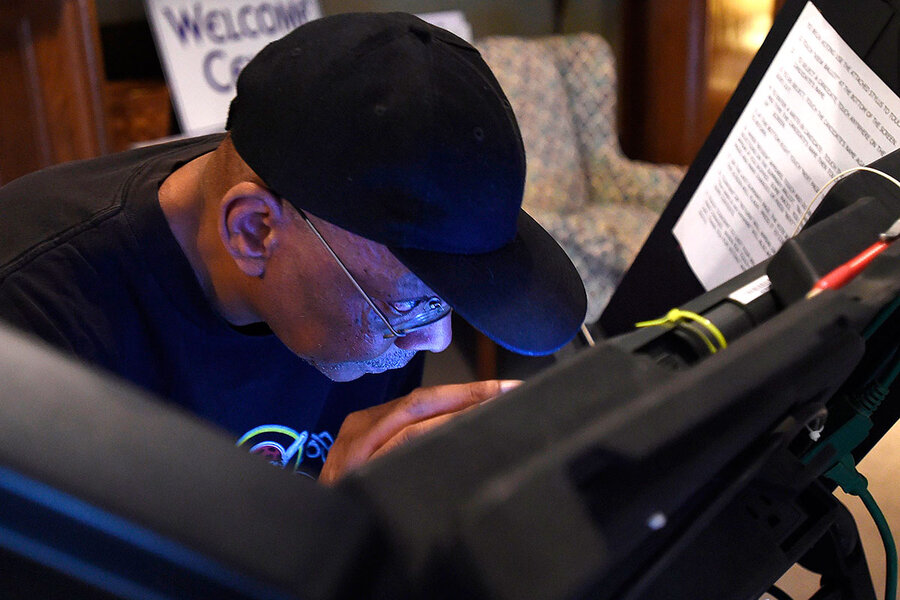
A paper record
For example, in 2016, 14 states were using voting machines incapable of producing a voter-verified paper record. Many of those states want to upgrade to a more secure voting system that would use paper ballots that can be hand-counted if there is a suspected breach or failure of tabulation software. But since the turmoil of 2016, only one of those states, Virginia, has made the transition to a more secure voting system.
Part of the reason for the delay is cost. It can cost tens of millions of dollars to outfit an entire state with new voting machines. Estimates are that Pennsylvania, a key swing state, may have to spend up to $60 million to replace its voting machines. Under the new federal grant, Pennsylvania is set to receive $13.5 million.
Officials in New Jersey and Georgia are actively exploring ways to buy new voting machines that support paper ballots. But they haven’t done so yet.
“It is disappointing that, given that there is pretty much uniform agreement among security experts that these systems need to be replaced, that we couldn’t manage to do it before the 2018 election,” Norden says.
Moreover, he and others are quick to point out that paper ballots alone won’t be enough to protect US elections.
Michigan has used voter-verifiable paper ballots with its voting machines since 2004. But last year, the state spent $40 million to purchase the newest version of its voting machines, with upgraded software and more robust security features. The upgrade involved replacing 5,000 machines in 4,300 voting precincts state-wide, according to state officials.
“We want to stay two steps ahead of the bad guys,” says Fred Woodhams, a spokesperson in the Michigan secretary of state’s office. “We are pleased about where we are, but we still have more work to do.”
Mr. Woodhams says Michigan was allocated $10.7 million of the $380 million in federal election security funds earlier this year. The state plans to use much of that money to hire a cybersecurity contractor to conduct a comprehensive review of the state’s election system.
“They will be looking at the whole system globally and at the local level as well,” he says. “Because there are a lot of systems that interface with each other, we wanted to see how everything works together, and where the vulnerabilities are.”
As in many states, Michigan’s election system is decentralized. Elections are conducted at the local level by 83 county clerks and 1,520 city and township clerks. While decentralization makes it harder for a hacker to disrupt or swing an election, it also makes it harder to provide a uniform defense against cyberthreats.
The same issue arises in Minnesota, where elections are run at the county level, but only nine of the state’s 87 counties are large enough to support a full-time, year-round clerk, according to Minnesota officials.
Security experts note that many election offices across the country, particularly in rural areas, do not have a single information technology specialist on staff, let alone someone trained in the latest cybersecurity threats and counter-techniques.
Following the 2016 election, many state and local election officials complained that the national government failed to provide them with real-time warnings about ongoing efforts to hack into their systems. In some cases, local officials didn’t learn of the attacks until 10 months later.
Since then, the Department of Homeland Security has set up an organization called the Election Infrastructure Information Sharing and Analysis Center. If state officials agree to participate, they can install monitors on their election networks to track and identify any potential threats. The center would then share recovered information and provide a warning system for other states.
Risk-limiting audits
Given the complexity of identifying and addressing election vulnerabilities, many election specialists advocate the use of audit techniques to help verify election results and identify hacking attempts.
Estimates are that 32 states have regulations or procedures for post-election audits. But many of these audits aren’t structured to detect a tabulation software flaw, or aren’t rigorous enough to uncover a deliberate hack, experts say.
The most robust audit available uses statistics to examine a random sample of paper ballots to verify the computer-driven tabulation of votes. Because it relies on a hand-count of a relatively small number of ballots (at least initially), these so-called risk-limiting audits provide a reliable way to double-check computerized election results.
The science has been proven and the cost is not substantial. But in 2018, Colorado will be the only state in the country using this technique to verify its elections.
“There is pretty much universal agreement that this is an important security measure to detect and perhaps recover from attacks on electronic voting systems,” Norden says. But he acknowledges: “There has been very little progress made on that front.”
Rhode Island is set to conduct risk-limiting audits starting in 2020. Pilot programs have been undertaken in Indiana and Orange County, Calif.
For the first time in 2018, Michigan will be conducting an audit of election results, by physically counting paper ballots in randomly selected precincts in each county.
“This is an avenue that might give assurance to people who are concerned about cybersecurity issues,” Woodhams says. “Every voter in Michigan will be using a paper ballot, so at the end of the day, even if everything goes wrong, we still have a paper ballot to take out and look at by hand if we have to.”
But while Michigan is ahead of many states, Woodhams acknowledges that protecting an election from outside interference will be an ongoing process.
“Cybersecurity isn’t something where you can declare victory and move on,” he says. “It is something you work on every day.”